NSA Leaks and the Future of Surveillance
- Posted on July 29, 2013 at 4:42 pm by gabe.
- 61 Comments
Authored by Gabe McCoy and Kevin Hamilton, mostly before the most recent revelations (and also heavily revised in light of them).
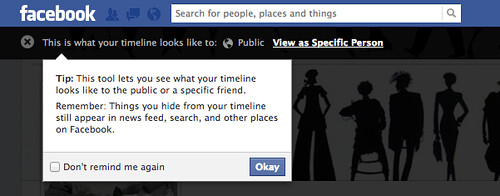
After the Snowden leaks about PRISM, we still don’t know much about exactly how the government is spying on its citizens. All signs point to a level of surveillance that is taking place deep inside realms we traditionally define as “private.”
One thing we know, however, is at least one approach the NSA is taking to the law, and this approach does not bode well for the future. Their argument suggests a much more conservative approach to privacy than they seem to have actually adhered to, if XKeyscore is working as advertised. But even if they “retreat” from the current level of snooping, to a level that conforms to their expressed standard, problems will remain. At the heart of their approach – and much of the outrage – is an inadequate approach to the definitions of private and public. (more…)